Safeguarding Digital Futures: The Uncomfortable Truths About Cyber Resilience in Education
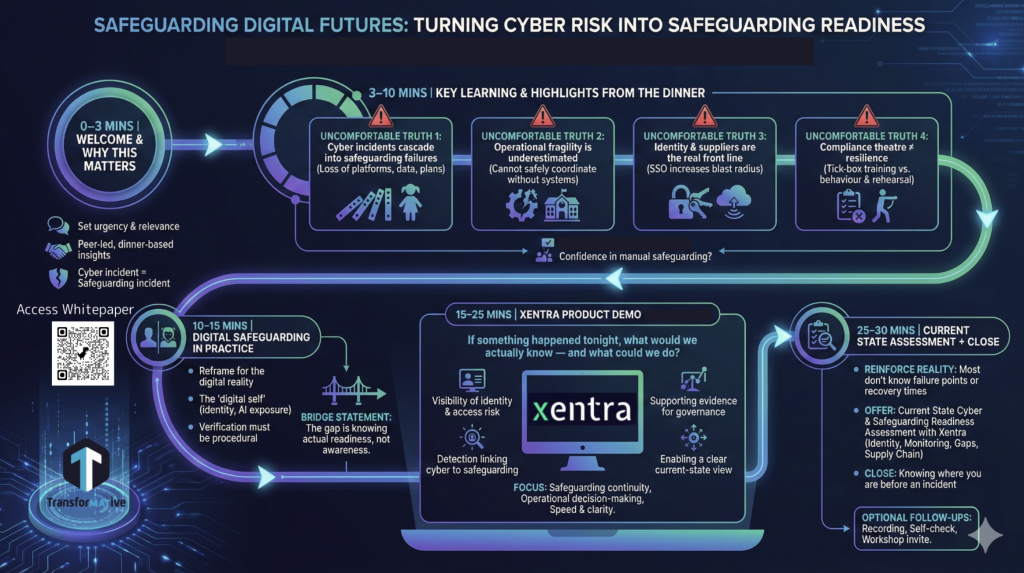
We recently brought together sector leaders and specialists for a webinar on cyber resilience in education. What emerged was not another technical conversation about firewalls and compliance checklists. It was a much more fundamental discussion about safeguarding.
If we are honest with ourselves, cyber security and safeguarding are no longer separate conversations. They are inseparable. And there are some uncomfortable truths that education leaders need to confront.
1. Cyber incidents become safeguarding failures
A serious cyber incident is not simply an IT problem. It is a safeguarding issue from the moment systems go down.
If a trust loses access to pupil data, care plans, safeguarding records or parental contact details, it loses its ability to coordinate support for vulnerable learners. If the systems that hold what many refer to as the grab bag are unavailable, staff cannot act with confidence or speed. That creates a material safeguarding risk.
Ransomware does not just lock files. It disrupts the operational fabric that protects children and staff. When we separate cyber risk from safeguarding risk, we create blind spots. They must be discussed together at board level, not in isolation.
2. We underestimate operational fragility
Many organisations still believe a cyber breach means a few days without laptops. The reality is far more complex.
A major ransomware attack can affect:
- Cloud-based telephony and critical communications
- Building Management Systems and door access controls
- Payroll and finance operations
- Catering systems and payment processes
If pupils cannot be charged for meals, the financial implications mount quickly. If access control systems fail, that becomes a site safety issue. If payroll is disrupted, staff confidence is damaged.
Modern education is deeply dependent on interconnected digital systems. Over time, workflows become automated and undocumented. When they fail, organisations discover just how much tacit knowledge has been embedded in technology. The gaps that appear are often deeper than expected.
Operational fragility is not theoretical. It is real, and it is growing.
3. Identity and suppliers are the real front line
The biggest risks are not always where we expect them to be.
Identity management has become central to how schools and trusts operate. Single Sign-On simplifies life for users and IT teams. But it also increases the blast radius. If one identity is compromised, access to multiple systems can follow.
We are also seeing compromised student accounts being used to phish staff and peers. That changes the threat model. The attacker no longer appears external. They appear familiar.
Then there is the supply chain. Catering providers, building management suppliers, outsourced services, all connecting devices and systems to the network. Each connection represents a potential entry point.
Too often, due diligence stops at contractual paperwork. Cyber maturity of suppliers is assumed rather than assured. In practice, that can leave an open door into core systems.
If we want to improve resilience, we need to treat identity and supplier governance as strategic priorities, not operational afterthoughts.
4. Compliance theatre is not resilience
Annual training sessions and policy sign-offs may satisfy an audit requirement. They do not create resilient organisations.
Ticking a box once a year is compliance theatre. It gives a sense of control without delivering it.
Real resilience is educational in the truest sense. It is:
- Continuous, delivered in small and regular interventions rather than a single annual event
- Contextual, grounded in real phishing attempts and real incidents experienced by the organisation
- Tested, using simulations and short assessments to identify higher risk users and support them properly
Cyber threats evolve constantly. Our approach to awareness must evolve too. If we treat it as a static compliance exercise, we will always be behind.
Moving from awareness to action
The conversation closed with a practical focus on partnership. Education organisations do not need more abstract guidance. They need accessible, specialist support that understands both safeguarding and cyber risk.
Models that provide enterprise-grade protection at a price point education can sustain are essential. The ambition should be simple. Deliver Tier 1 capability at Tier 3 commercials so that strong cyber resilience is not a luxury, but a baseline.
Transformation in education is digital by definition. Safeguarding in education must now be digital by design.
If we are serious about protecting learners and staff, cyber resilience has to move from the IT agenda to the leadership agenda. That is where real change begins.